This article was automatically translated from the original Turkish version.
Kerberos is a cryptographic protocol used for authentication in computer networks. It enables users or services to securely verify each other’s identities. Its primary purpose is to prevent passwords or identity credentials from being intercepted by third parties in an untrusted network environment.
Kerberos was developed in the 1980s as part of Project Athena at the Massachusetts Institute of Technology (MIT). MIT designed this protocol to provide centralized authentication in multi-user distributed systems. It is written in the C programming language. The initial version, Kerberos V4, was gradually replaced by the more advanced Kerberos V5 due to its limited security features. Kerberos V5 is defined in RFC 4120, published by the Internet Engineering Task Force (IETF) in 2005 (IETF, 2005).
The name Kerberos is derived from Cerberus, the three-headed dog of ancient Greek mythology. Cerberus guards the gates of the underworld and prevents the dead from escaping. During its development at MIT, this mythological figure was chosen as a symbolic representation of a guardian that blocks unauthorized access and controls secure passage.
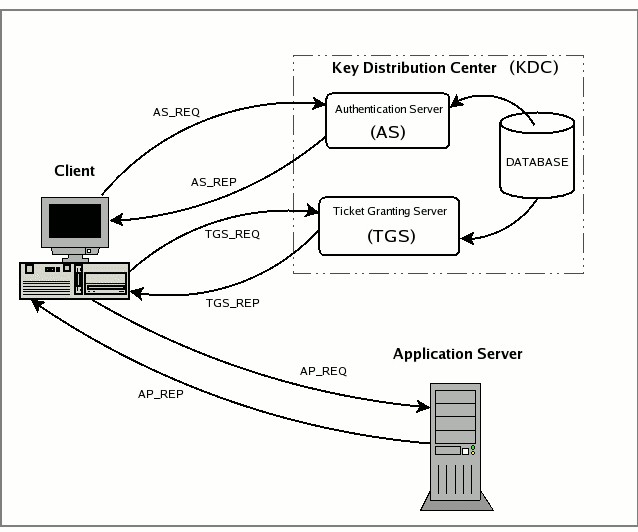
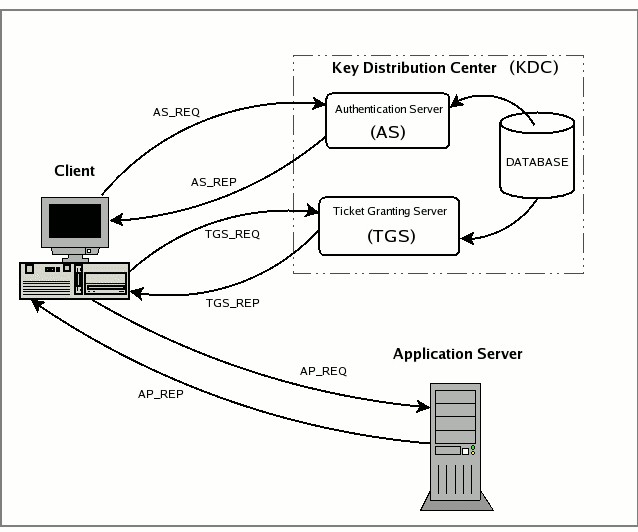
Kerberos uses symmetric key cryptography and operates with three main components:
The process works as follows:
In this system, credentials are not transmitted with every service request; instead, a ticket-based mechanism is used.
In the Kerberos protocol, tickets used during authentication are categorized into three main types: initial tickets obtained at login, renewable tickets whose validity can be extended, and forwardable tickets that can be transferred to other systems.
The Kerberos protocol relies heavily on timestamps for security. Therefore, the time difference between clients and servers must not exceed five minutes. This requirement necessitates the use of synchronization mechanisms such as the Network Time Protocol (NTP).
Kerberos is supported by many operating systems and network services, most notably as the underlying authentication mechanism in Windows Active Directory. Microsoft has used Kerberos V5 as its authentication protocol in Active Directory since Windows 2000. On Linux and Unix-based systems, open-source implementations such as MIT Kerberos and Heimdal are widely used. Additionally, Kerberos can be employed via GSS-API (Generic Security Services Application Program Interface) to develop secure network applications.
The Kerberos protocol enables users to securely log in to multiple services without re-entering passwords, thanks to features such as centralized authentication management and single sign-on (SSO), while relying on a symmetric key cryptography-based security infrastructure. However, for the system to function correctly, strict time synchronization between clients and servers is essential; failure to maintain this synchronization can cause authentication failures. Furthermore, if the central Key Distribution Center (KDC) becomes unavailable, authentication across the entire system is impossible. Additionally, because Kerberos uses only symmetric encryption, careful and secure key management is mandatory.
No Discussion Added Yet
Start discussion for "Kerberos Communication Protocol" article
Working Principle
Protocol Operation
Security Features
Usage Areas and Applications