(Generated by AI)
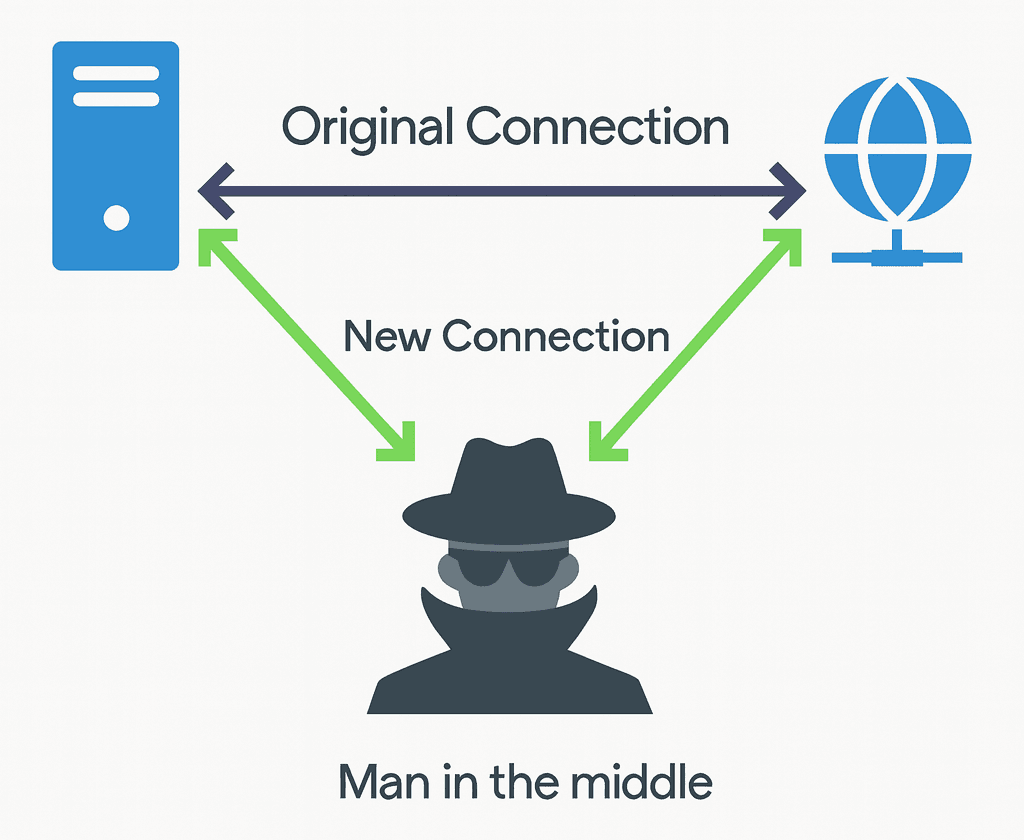
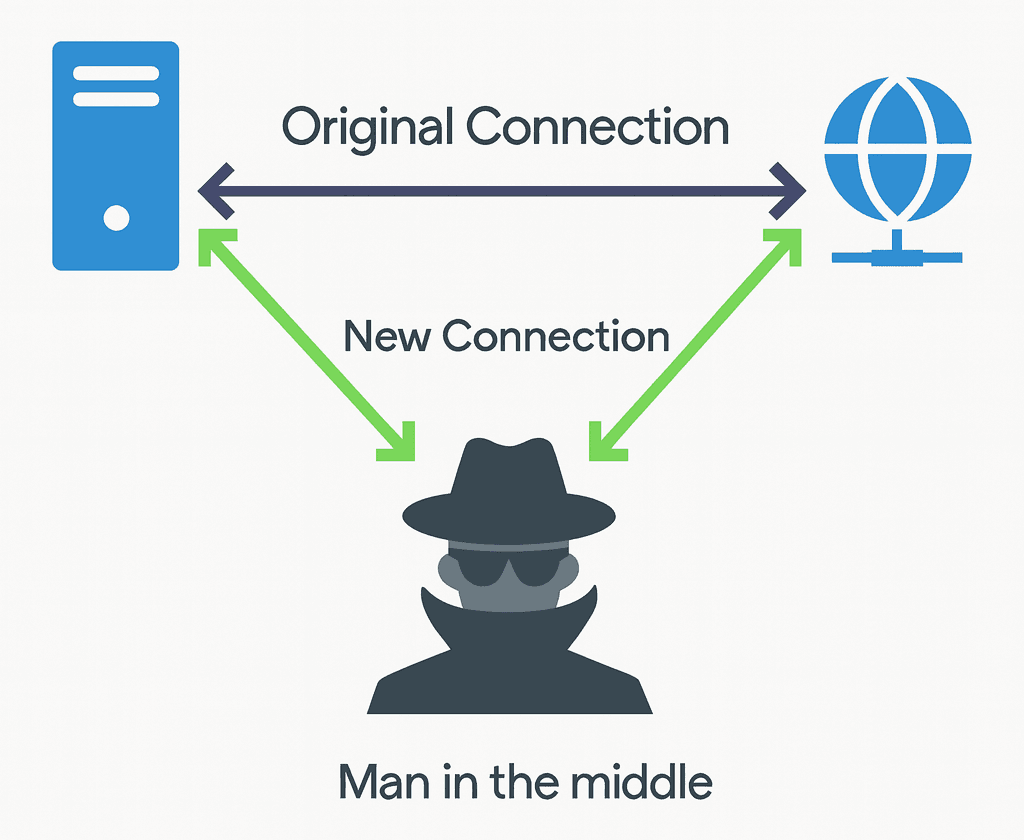
A Man-in-the-Middle (MitM) attack is a cyberattack in which a malicious actor secretly intercepts and potentially alters the communication between two parties who believe they are directly communicating with each other. The attacker positions themselves between the victim and the intended destination to eavesdrop, steal sensitive data, inject malicious content, or impersonate one of the parties.
The concept of interception in communications has existed long before digital networks, dating back to military codebreaking and wiretapping during the early 20th century. With the rise of the internet in the 1990s, digital MitM attacks emerged as attackers exploited weaknesses in unencrypted traffic. The evolution of wireless technology and public Wi-Fi further expanded opportunities for attackers.
MitM attacks generally occur in unsecured or poorly protected communication channels. The attacker typically inserts themselves into the data flow by exploiting weaknesses in network protocols, insecure Wi-Fi connections, or session handling. Once in position, the attacker can monitor traffic, capture credentials, manipulate transmitted data, or redirect users to fraudulent websites.
MitM attacks can have severe consequences for individuals and organizations, including:
Attackers often rely on specialized tools to execute MitM attacks. The most commonly used include:
These tools are often also used by penetration testers and researchers for legitimate purposes, but in the hands of attackers, they become powerful weapons for compromising data security.
Defending against MitM attacks requires a layered security approach:
Contrast Security. “Man-in-the-Middle Attack.” Accessed August 5, 2025. https://www.contrastsecurity.com/glossary/man-in-the-middle-attack
CrowdStrike. “Man-in-the-Middle (MitM) Attack.” Accessed August 5, 2025. https://www.crowdstrike.com/en-us/cybersecurity-101/cyberattacks/man-in-the-middle-mitm-attack/
Dergipark. “Man in the Middle (MitM) Attack.” Accessed August 5, 2025. https://dergipark.org.tr/tr/pub/ejosat/article/1187984
ESET. “Man-in-the-Middle.” Accessed August 5, 2025. https://help.eset.com/glossary/tr-TR/man_in_the_middle.html#:~:text=Breadcrumb'lar&text=Ortadaki%20adam%20(MITM)%2C%20bir,de%C4%9Fi%C5%9Ftirdi%C4%9Fi%20bir%20siber%20sald%C4%B1r%C4%B1%20t%C3%BCr%C3%BCd%C3%BCr
Fortinet. “Man-in-the-Middle Attack Definition.” Accessed August 5, 2025. https://www.fortinet.com/resources/cyberglossary/man-in-the-middle-attack#:~:text=Man%2Din%2Dthe%2DMiddle%20Attack%20Definition,communication%20channel%20to%20steal%20data
Guney Bilişim. “Ortadaki Adam Saldırısı (MiTM) Nedir?” Accessed August 5, 2025. https://www.guneybilisim.com/ortadaki-adam-saldirisi-mitm-man-in-the-middle-nedir
IBM. “Man-in-the-Middle.” Accessed August 5, 2025. https://www.ibm.com/think/topics/man-in-the-middle
İnönü University – Cyber Security. “Man-in-the-Middle (MitM) Attack: What Is It and How Is It Performed?” Accessed August 5, 2025. https://siber.inonu.edu.tr/man-in-the-middle-mitm-saldirisi-nedir-nasil-gerceklestirilir/
Kaspersky. “Man-in-the-Middle Attack.” Accessed August 5, 2025. https://encyclopedia.kaspersky.com/glossary/man-in-the-middle-attack/
MBR Teknoloji. “Ortadaki Adam Saldırısı (MitM) Nedir?” Accessed August 5, 2025. https://mbrteknoloji.com.tr/ortadaki-adam-saldirisi-mitm-nedir/
TechTarget. “Man-in-the-Middle Attack (MitM).” Accessed August 5, 2025. https://www.techtarget.com/iotagenda/definition/man-in-the-middle-attack-MitM
BeyazNet. “Ortadaki Adam (MitM) Saldırısı Nedir?” Accessed August 5, 2025. https://www.beyaz.net/tr/guvenlik/makaleler/ortadaki_adam_mitm_saldirisi_nedir.html
(Generated by AI)
No Discussion Added Yet
Start discussion for "Man-in-the-Middle (MitM) Attack" article
History
How It Works
Common Techniques
Potential Consequences
Tools Used in Man-in-the-Middle (MitM) Attacks
Notable Cases
Prevention and Defense
This article was created with the support of artificial intelligence.