This article was automatically translated from the original Turkish version.

In today’s world, network technologies have become one of the most essential infrastructures enabling communication among individuals and institutions. Now, it is not just computers but smartphones, tablets, smart systems, and even industrial machines that are connected to the internet. According to research, the number of internet-connected devices worldwide is expected to reach 50 billion by 2025. This development further underscores the critical role networks play in our lives.
Networks are structures that enable data exchange and consist of specific components. These components can be grouped under three main categories:
End devices are the devices directly accessed by users on a network. They communicate via IP addresses and perform the fundamental functions of the network.
Examples of end devices include:
These devices serve as the origin or destination of data within the network. For example, when an employee connects to a company server or a smartphone accesses the internet via Wi-Fi, end devices are being used.
Intermediary devices are responsible for directing and transmitting data across the network.
Devices in this category include:
For example, in a company office where multiple computers and printers share the same network, a switch (key) is used to connect these devices. If the company needs to secure its internet connection, a firewall (firewall) is deployed.
Media is the component that determines how data is physically transmitted across a network. It defines the method by which data is conveyed and can take three distinct forms:
What is End Device
Networks are classified into different categories based on their size, purpose, and the areas they cover.
A LAN is a type of network that connects devices within a limited area. It is commonly used in homes, offices, schools, and small businesses (common).
Characteristics:
A WAN is a larger network that connects multiple LANs. For example, the internet (enormous) is a WAN.
Characteristics:
What Is WAN? LAN vs. WAN - Huawei
In designing a robust network, the following four elements must be considered:
Network technologies are continuously evolving and adapting to new trends:
Network communication is not achieved merely by connecting hardware; it requires devices to exchange data according to specific rules. Computers, phones, and other network devices use certain protocols and models to communicate with each other. This section will examine the importance of network protocols, reference models, and data encapsulation processes.
For networks to function properly, specific rules must be established. These rules define how communication occurs, ensuring devices can interact seamlessly. The rules defined by network protocols consist of the following components:
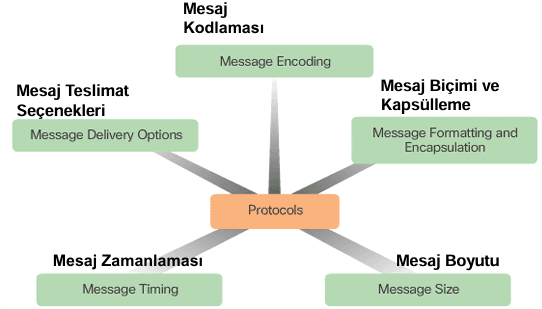
Protocols Requirements
For two or more devices on a network to communicate without issues, they must adhere to a defined set of rules. This entire set of rules is called a protocol. Protocols are standards that determine how messages are sent, received, and interpreted.
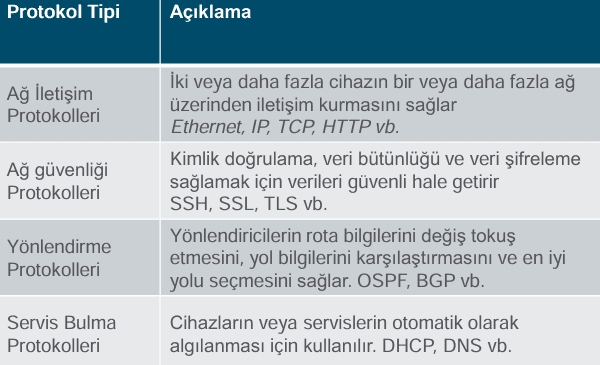
Some commonly used protocols in network communication include:
These protocols determine how devices create, transmit, and interpret data packets.
Protocols
Network communication does not occur through a single protocol. Various protocols work together to form a more comprehensive and functional building. These groups of protocols are called protocol suites.
1. TCP/IP Protocol Suite: Forms the foundation of the internet and is divided into four main layers:
2. OSI Protocol Suite: This seven-layer model was developed to ensure interoperability between systems from different manufacturers. OSI model provides a structure covering all stages from physical connections to the application level.
3. AppleTalk: A protocol suite developed by Apple, specifically designed for Apple devices. It enabled communication among Macintosh computers before the widespread adoption of IP.
4. Novell NetWare: A network operating system protocol suite developed by Novell, based on IPX/SPX protocols. It was widely used in LAN-based networks.
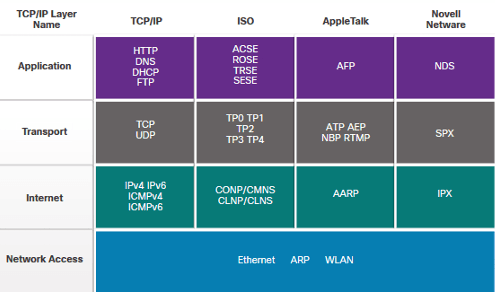
Network Protocols - Cisco
To better understand how communication occurs in networks, various models have been developed. The most widely known are the OSI Model and the TCP/IP Model.
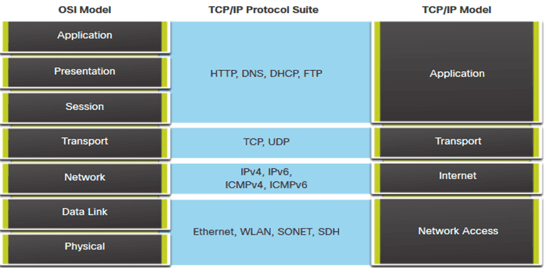
OSI vs TCP/IP - Cisco
The OSI model provides an open standard by dividing network communication into seven layers:
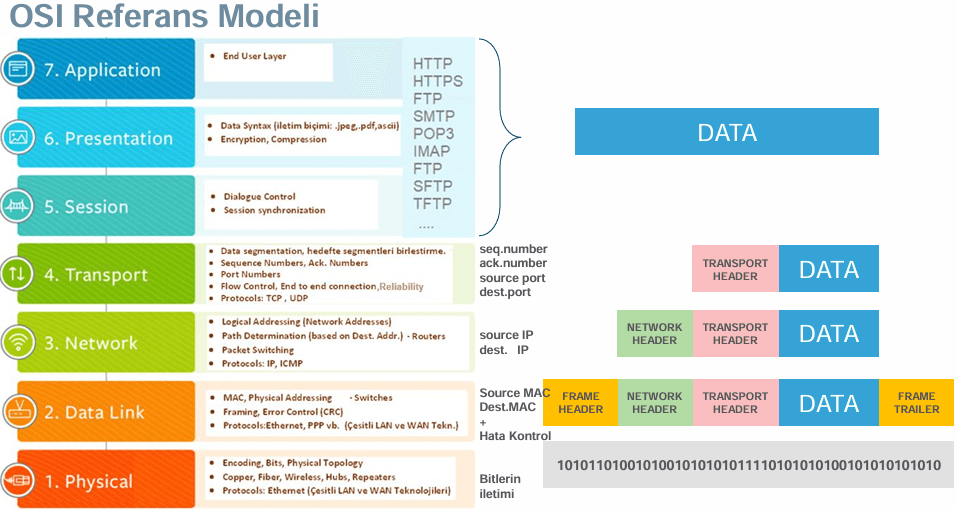
OSI Model - Cisco
The TCP/IP model, which forms the foundation of the internet, has a simplified structure compared to the OSI model and consists of four layers:
The OSI model provides a theoretical framework, while the TCP/IP model is an active system used in the real world. The TCP/IP model is more widely used than OSI because it was developed as the foundational protocol suite of the internet.
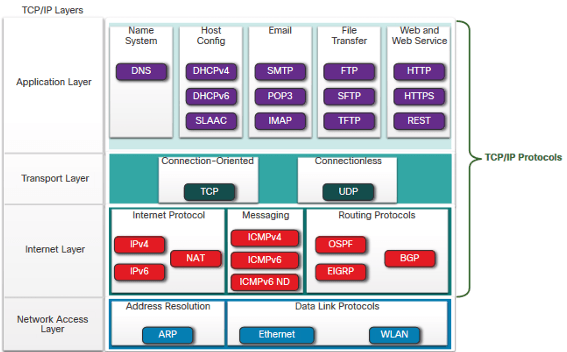
TCP/IP Layers - Cisco
Before data is transmitted across a network, it undergoes a process called encapsulation. During this process, each layer adds its own header to the data to ensure seamless communication. The data encapsulation process consists of the following stages:
On the receiving device, this process process is reversed to restore the data to its original form.
"CCNA 1 v7.0 Curriculum: Module 1 - Networking Today." *IT Exam Answers*. Accessed February 16, 2025. https://itexamanswers.net/ccna-1-v7-0-curriculum-module-1-networking-today.html
"CCNA 1 v7.0 Curriculum: Module 2 - Basic Switch and End Device Configuration." *IT Exam Answers*. Accessed February 16, 2025. https://itexamanswers.net/ccna-1-v7-0-curriculum-module-2-basic-switch-and-end-device-configuration.html
"CCNA 1 v7.0 Curriculum: Module 3 - Protocols and Models." *IT Exam Answers*. Accessed February 16, 2025. https://itexamanswers.net/ccna-1-v7-0-curriculum-module-3-protocols-and-models.html

No Discussion Added Yet
Start discussion for "Network Administration" article
Basic Components of Networks
End Devices
Intermediary Devices
Media
Network Types and Applications
Local Area Network (LAN)
Wide Area Network (WAN)
Foundational Principles of Reliable Networks
1. Fault Tolerance
2. Scalability
3. Quality of Service (QoS)
4. Security
Network Trends: Technologies of the Future
Protocols and Models in Networks
Rules in Network Communication
Network Protocols
Basic Network Protocols
Protocol Suites
Common Protocol Suites
OSI and TCP/IP Models
OSI Model (Open Systems Interconnection)
TCP/IP Model
Data Encapsulation Process